

This article explains approaches to strengthening governance for cloud security when workloads and data are hosted on the Google Cloud service suite. It describes the concept of aligning organizational policies, technical controls, and operational processes so that cloud resources are managed consistently and risks are assessed continuously. The discussion focuses on governance structures, control families, and measurable activities that commonly appear in organizational efforts to reduce misconfiguration, enforce access controls, and maintain visibility over cloud environments.
Governance in this context typically covers policy definition, assignment of responsibilities, enforcement mechanisms, monitoring, and review cycles. It may include mapping organizational roles to cloud identity constructs, creating constraints at the resource hierarchy level, and defining detection and response capabilities. The emphasis is on creating repeatable, observable patterns that can be integrated into development and operations workflows and that support compliance and risk management objectives without implying guaranteed outcomes.

Identity and access controls form a core example of governance because they determine who or what can act on cloud resources. In practice, organizations may use role-based models, scoped service accounts, and short-lived credentials to reduce standing privileges. Access reviews and automated policy checks can be integrated into identity lifecycles. These approaches typically aim to limit exposure by aligning cloud identities with organizational roles and by capturing access events in audit logs for later review.
Resource hierarchy and policy constraints illustrate how governance can be applied at scale. By grouping projects under folders and an organization node, teams can attach constraints that prevent certain configurations, such as disabling public IPs or restricting region placement. Policy-as-code approaches may be used to codify constraints and validate deployments before they reach production. Such structures often help teams enforce baseline settings consistently while allowing controlled exceptions where necessary.
Network and perimeter controls are another governance dimension that commonly receives focused attention. Segmentation, private connectivity options, and perimeter services can be used to reduce exposure of sensitive workloads. Control implementations often include firewalls, service perimeters, and private access paths that work together with identity controls. Network governance typically includes documented patterns for segmentation and testing procedures to validate isolation objectives.
Monitoring and threat detection complete the governance loop by turning observable events into signals for action. Centralized collection of logs, metrics, and configuration snapshots may be used to assess posture and detect anomalies. Security posture tools may provide inventories of misconfigurations and known exposures, while alerting pipelines route incidents to response teams. Governance arrangements often specify retention, access to forensic records, and periodic review intervals aligned with organizational risk tolerance.
In summary, strengthening governance for cloud security on the Google Cloud service suite typically involves coordinating identity controls, resource-level policies, network segmentation, and monitoring into a cohesive program. Each component may be implemented using policy-as-code, automated validation, and defined operational roles so that changes can be tracked and reviewed. The next sections examine practical components and considerations in more detail.
A clear identity and access governance model on Google Cloud may begin with mapping organizational roles to cloud identities and defining a lifecycle for those identities. Common elements include role separation between administrative and operational functions, use of service accounts for machine identities, and mechanisms for granting temporary or scoped access. Organizations often track access via audit logs and may use automated processes to revoke stale privileges. Identity governance typically seeks to balance operational needs with the principle of least privilege while keeping auditability and reversibility in view.
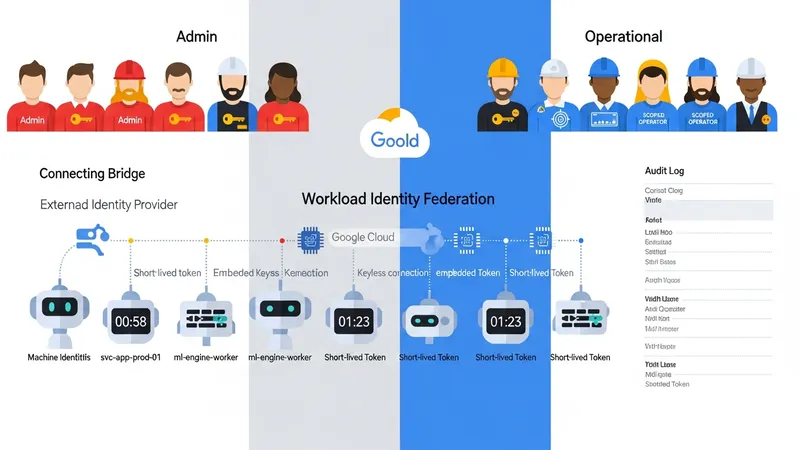
Service accounts and workload identities can be managed to reduce long-lived credentials and to enable fine-grained permissions for automated workflows. Patterns that are often employed include unique service accounts per workload, use of short-lived tokens, and constrained scopes for permissions. Workload identity federation or comparable approaches may be used to avoid embedding static credentials in code or artifacts. These measures commonly reduce the window of exposure if credentials are compromised and support more predictable access control.
Role design is a practical consideration; predefined roles, primitive roles, and custom roles each present trade-offs. Predefined roles may map to common cloud functions, while custom roles allow organizations to tailor privileges more closely to business tasks. Governance programs commonly include processes for creating and approving custom roles, documenting intended use, and periodically reviewing role assignments. Role assignment patterns may also be combined with groups or external identity providers to streamline administration at scale.
Operational considerations include automating access reviews, enabling detailed audit logging, and integrating identity events with alerting and ticketing systems. Periodic certification processes and emergency access procedures are often documented so that governance teams can respond to incidents while maintaining traceability. These considerations may be expressed in policy documents and supported by tooling that enforces and reports on access-related requirements.
Network governance frequently focuses on establishing segmentation and minimizing public exposure of services. Typical constructs include virtual private clouds with subnetting, network firewalls, and route controls that together define traffic boundaries. Organizations may adopt patterns for isolating environments such as development, staging, and production, and for restricting cross-project traffic. These patterns often combine with identity controls to ensure that network-level protections complement access policies rather than replace them.
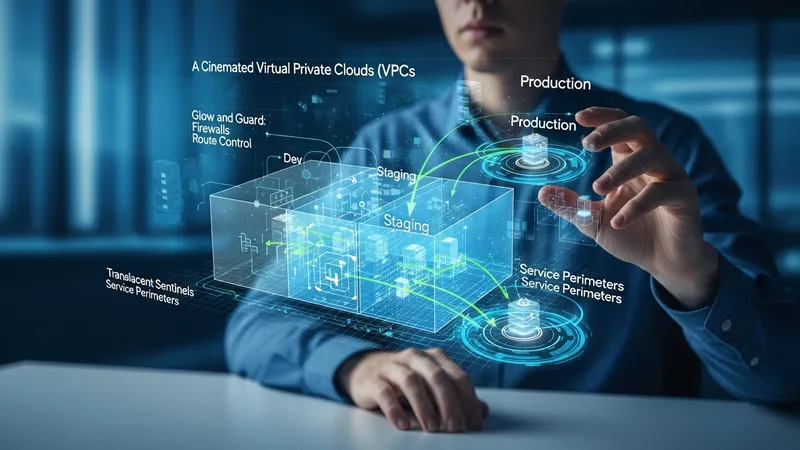
Perimeter controls may be implemented to constrain data egress and to limit access to managed services. Examples of control patterns include service perimeters or private connectivity mechanisms that restrict interactions between projects or external networks. Such perimeters commonly aim to reduce unintended data exfiltration and to enforce regulatory or internal constraints on where data may be accessed. Perimeter design is often influenced by application architecture and data classification policies.
Firewall rules, routing policies, and load-balancing configurations are operational elements that may be governed through standardized templates and automated deployment pipelines. Infrastructure as code approaches can be used to version network configurations and to run pre-deployment checks against policy constraints. Governance frameworks may specify acceptable default rules, required exceptions processes, and test procedures to validate that network segmentation meets stated objectives.
Testing and validation are typical governance activities for network controls. Organizations may schedule regular vulnerability scans, configuration audits, and segmentation tests to confirm the effectiveness of perimeter defenses. Findings from these activities often feed back into governance cycles to refine policies and to update templates or constraints. This feedback loop helps maintain alignment between architectural changes and governance expectations.
Centralized collection and retention of telemetry are commonly recommended elements of cloud security governance. Logs from identity systems, resource changes, and network flows may be aggregated into a central repository where they can be searched, correlated, and retained according to policy. Retention periods and access controls for telemetry are typically defined in governance documents so that audit and forensic needs can be met while managing storage considerations.

Detection capabilities often combine rule-based alerts and anomaly detection that monitor for known indicators of misconfiguration or compromise. Security posture assessments may generate inventories of exposed resources and known misconfigurations that require remediation. Governance arrangements commonly define severity levels, escalation paths, and coordination protocols so that events progress through defined handling processes rather than ad hoc responses.
Integration with incident response tooling and operational workflows is a common governance concern. Alerts may be routed to on-call teams, ticketing systems, or orchestration platforms that help coordinate containment and remediation activities. Forensic data collection, such as preserved logs and snapshots, is often organized so that investigations can be conducted with minimal impact to production systems while preserving chain-of-custody where required.
Periodic review of detection rules, alert thresholds, and telemetry sources is often included in governance cycles to reduce false positives and to adapt to evolving architectures. Metrics about mean time to detect and mean time to acknowledge may be tracked as part of performance measurement, and those metrics can inform adjustments to tooling or staffing. These practices typically support continuous improvement of monitoring and response capabilities.
Policy governance often comprises written policies that define permitted configurations, data handling requirements, and responsibilities for controls. These policies may be enforced through automated policy-as-code tools that validate deployments against constraints prior to provisioning. Governance programs typically document exception processes, required evidence for compliance, and review cadences so that exceptions are traceable and time-limited rather than open-ended.
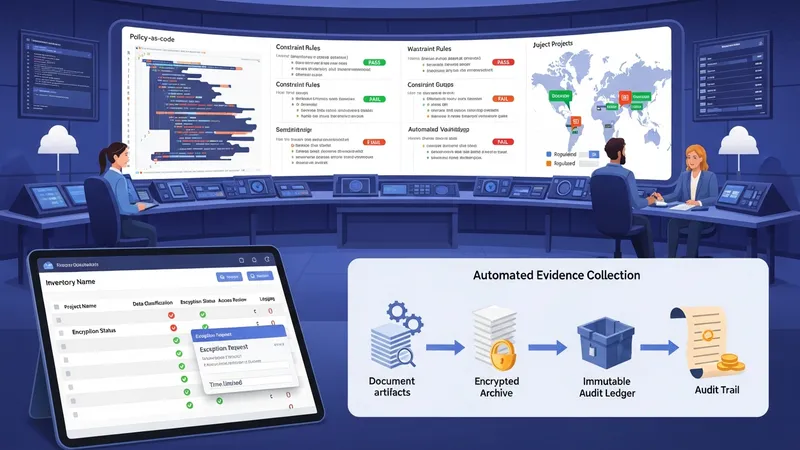
Compliance mapping and evidence collection are practical governance activities used to demonstrate alignment with external frameworks or internal standards. Organizations commonly maintain inventories of which projects contain regulated data and automate evidence collection for controls such as encryption, access reviews, and logging. This approach aims to reduce manual effort during audits while keeping the scope of compliance efforts aligned with organizational priorities.
Operational governance also addresses change management, release controls, and configuration drift. Processes that require code review, automated testing, and staged rollouts may be used to reduce the likelihood of misconfiguration reaching production. Governance documents often define responsibilities for approving changes, performing post-deployment validations, and rolling back when necessary, so that operational actions remain auditable and consistent with risk tolerance.
Governance programs commonly include continuous improvement mechanisms: policy revisions, lessons learned from incidents, and periodic maturity assessments. Measurement and reporting may focus on configuration compliance rates, frequency of exceptions, and time to remediate identified issues. These measures can help governance stakeholders understand trends and prioritize areas where additional controls or resources may be warranted, without implying guaranteed outcomes.